Global events continue to increase the requirement for security in applications ranging from defense and aerospace to communications and electronic storage. Security solutions have been refined over the past half- century and are just now appearing on the popular Processor PMC (PrPMC) building blocks. This article uses application examples to describe encryption options and how these new PrPMC "macro-components" can simplify and speed deployment of secure products in VME architectures.
Rapid development continues to be the mantra for companies developing embedded VME products. PrPMCs have been accepted as small, fast, and flexible standard-based method of adding computing elements for these demanding applications. Global events have highlighted a new dimension of computing technology, refocusing the requirement for increased security in the defense and aerospace market, which is also influencing other industries. Telecom, of course, is right in the middle of these concerns, as is banking, electronic storage systems, and in the near future even medical imaging, due to the Health Insurance Portability and Accountability Act (HIPAA) of 1996. Further examination discloses that the flexibility and rapid development advantages of PrPMCs with security capabilities are an ideal building block addressing the evolving need for security as well as the insatiable demand for increased computational capabilities with 1+ GHz PowerPC CPUs.
When asked why OEMs prefer standards-based PrPMCs for VME performance upgrades, the repeated responses are size, speed, and flexibility. For example, defense and aerospace, telecom, and all embedded providers are looking to this compact form factor for a small CPU and memory subsystem, which can easily be added to the estimated 100,000+ PMC sites on the VME market. PrPMCs enable two alternatives to increase computing performance: a higher performance PrPMC can replace an existing one with a slower CPU or less memory, or they can be added to existing applications to expand loosely coupled multiprocessing options. In today’s telecom environment, with downsized engineering, add-in performance and/or feature updates to existing VME-based product may be preferred to a complete resource intensive redesign. Flexibility is the third key benefit of these macro components, due to a wide range of available PrPMCs that allow the CPU, clock, and memory size that best matches the performance and cost goals for each model in a product family. In addition to these advantages, a dynamic product family defined by an industry standard and actually supported by multiple vendors provides a variety of choices and peace of mind. For those not familiar with PrPMC technology, the sidebar provides a summary describing highlights of the VITA 32 standard. But what about the addition of security to these popular building blocks?
Common security goals
Data traversing today’s telecommunications infrastructure is highly susceptible to interception for eavesdropping or modification. Both the data and control plane have vulnerabilities that can be exploited. Malicious parties may focus on stealing confidential data as it moves between telecommunications nodes, or they may directly attack a node, causing performance degradation or complete failure. The rapid dissemination of hacking tools and techniques increase the rate at which infrastructure vulnerabilities are maliciously exploited by vandals, thieves, and potentially, terrorists. As the rate of attack goes up, so does end-customer awareness of the current infrastructure’s weakness and their demand for a solution.
In telecommunications, a system could be considered reasonably secure if it has the ability to positively identify the sender and receiver, and guarantee the confidentiality and integrity of data transmissions while meeting the availability demands of its users. Table 1 provides a brief summary of these security goals.
Identification (authorization) is a potent defense against control plane attacks, since malicious parties often masquerade as other network nodes or remote system administrators, when attempting to disable a network. Passwords, digital certificates, and other digital "secret handshakes" are typical authentication schemes and the strongest are based on Public Key Cryptography.
Identifying and authorizing legitimate parties is important, but to prevent malicious outsiders from intercepting legitimate messages and substituting them with damaging content, the integrity of a message must be validated before accepting it. When sending a message, the authorized sender must calculate a specially designed Message Integrity Code (MIC), which is then appended to the message. The receiver knows how to calculate the same MIC, and can verify that the received message was not altered in transit. Any message with a MIC that does not match the message causes the message to be discarded. MICs (also know as Message Authentication Codes or MACs) are based on cryptographic hashing algorithms using shared secret keys. When used properly, message integrity is a formidable barrier to attacks against the control and data plane.
Authentication as well as integrity checking prevents attackers from bringing down a network or corrupting the data being transmitted over it. Confidentiality, a third security category, prevents outsiders from understanding the contents of a message. Confidentiality is synonymous with encryption, which as the name implies, is a cryptographic technique for rendering data unreadable to anyone who does not have the decryption key.
Taking a closer look
Modern encryption algorithms are so effective that an attacker has an equal chance of guessing the contents of a message as guessing the decryption key when communication between two endpoints is secured via encryption. That communication is said to be tunneled through the public communications network. IPSec and SSL are two tunneling protocols in widespread commercial use used to reduce attacks against telecommunications infrastructure. Recognizing this, many telecommunications vendors and third parties offer IPSec and SSL protocol stacks as software upgrades. While effective in thwarting attacks, running IPSec and SSL on general-purpose hardware has a very detrimental effect on system performance. A router normally capable of forwarding hundreds of megabits per second of "clear traffic" can seldom manage 5 Mbytes/sec of IPSec packets. If the control plane of a telecom switch is already reasonably loaded, forcing the control processor to decrypt less than 1 Mbyte/sec can interfere with normal call processing. The best way to restore system performance is to offload the CPU with a special purpose crypto-accelerator.
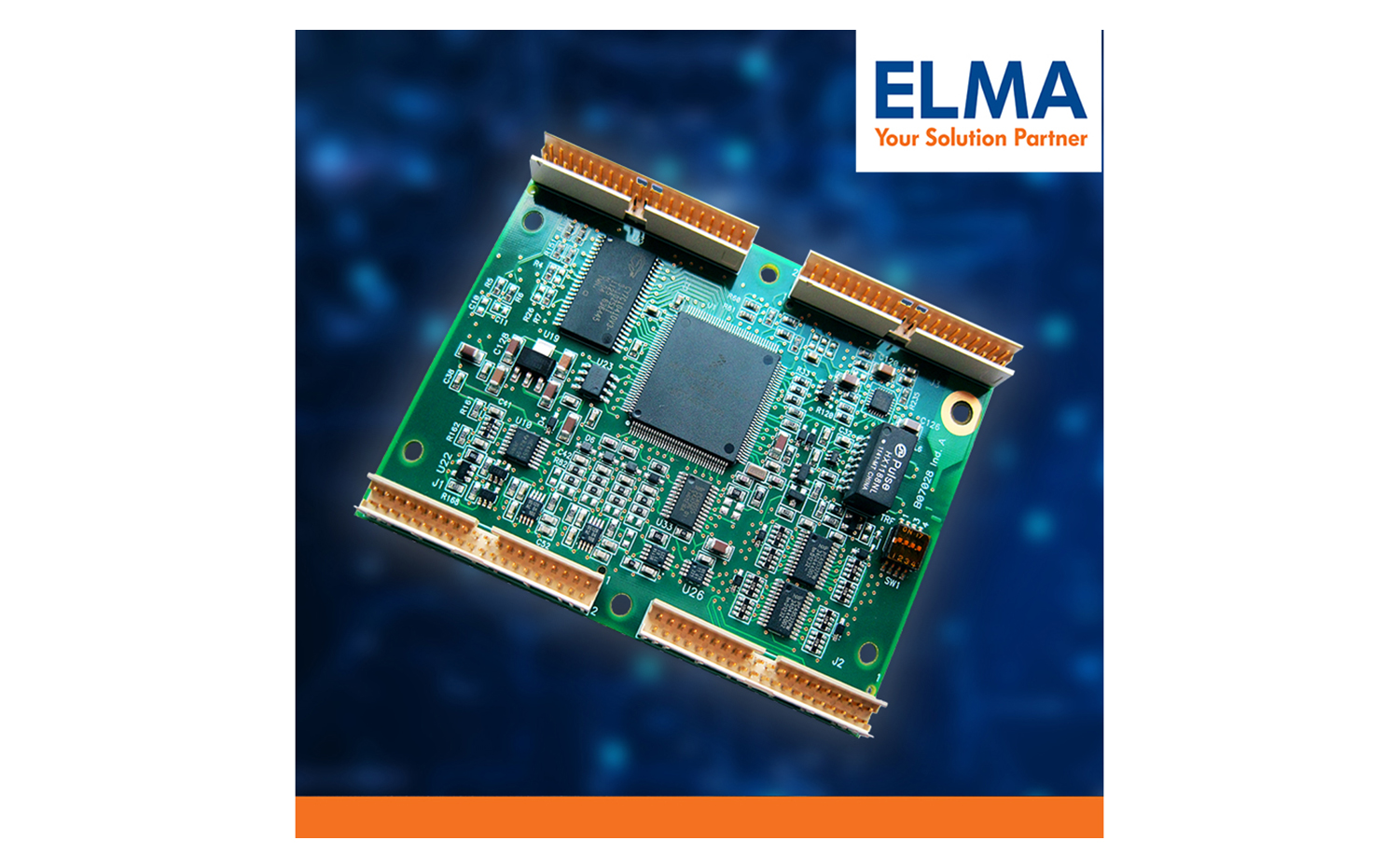
Many of the roles performed by PrPMCs can be substantially enhanced by crypto-acceleration. For this reason, the Motorola PrPMC815 includes the MPC185, a commercially available security co-processor developed by Motorola’s Semiconductor Product Sector. Applications or RTOS protocol stacks running on the host PowerPC processor can substantially reduce processor loading and increase tunnel throughput by offloading cryptographic authentication, integrity checking, and confidentiality algorithms – ultimately all four categories defined in Table 1. Figure 1 lists recommended security support for a variety of applications. Figure 2 shows a block diagram of a typical security-enabled PrPMC. The MPC185’s breadth of algorithm coverage and flexible programming model enables PrPMC815-based systems to address a wide range of security conscious control and data plane applications, such as 3G radio node controller, host bus adapter for storage, and secure control processor. Other traditional PrPMC applications are in no way diminished by this security functionality, and networked end points that have traditionally relied on the external appliances for security (e.g., medical imaging equipment, high-end industrial control systems) can now interface directly to the network via a secure connection.
In 2/2.5G networks, traffic is secured between the mobile station (MS) and the base transceiver station (BTS). In a 3G cellular network, voice and data traffic securely tunnel between the MS and the radio node controller (RNC). 3G networks also support much higher data rates than 2/2.5G and as a result, RNCs must have significantly greater processing power than a 2/2.5G Base Station Controller (BSC), particularly in the area of security processing. The Kasumi F8 and F9 algorithms provide 3G security, with F8 encrypting the messages and F9 performing integrity checking. RNCs also communicate with other RNCs and AAA servers and these communication channels are typically secured with IPSec. Due to its small size and ability to terminate both 3G MS-to-RNC tunnels and RNC-to-RNC IPSec tunnels, PrPMCs with crypto-acceleration are uniquely suited for RNC applications.
Another emerging standard with significant tunneling requirements is iSCSI, or SCSI over IP. SCSI is a higher layer protocol used between computers and closely attached storage systems. The growth of network attached storage (NAS) has been fueled by communication protocols that allow storage systems to be physically remote from the user in a consolidated location. I/O boards which connect a storage array to the LAN are referred to as host bus adapters and flexible PrPMCs with security include all the features necessary for a good host bus adapter that can be configured on a VME control board, as shown in Figure 3.
Existing and emerging telecommunications nodes, such as media gateways and multi-service access points, can generate significant amounts of control traffic, which may need to be tunneled. But of even greater concern can be the computational load associated with processing the messages themselves. H.323 and Session Initiation Protocol both have security extensions that use digital certificate exchange, which relies on cryptographically strong identification and authorization protocols. Signing or verifying a digital certificate is another area where the off-load capabilities of a security co-processor allow more cost effective use of more appropriate CPUs.
The key areas to consider when evaluating a security co-processor are, ultimately, the breadth of security protocols as well as the interface to the processing core. Typical interfaces to these crypto-engines include PCI, high-speed interfaces, or processor buses. Due to reduced pincount demands on the CPU, yet high-performance access to memory, the MPC185’s direct interface with the 60X processor/memory bus reduces system latency and increases overall system throughput yet still fits on the compact PrPMC form factor.
Conclusion
High walls can’t guarantee that a clever enemy won’t take a castle. Gatekeepers can be bribed and Trojan Horses now exist in other forms. Encryption solutions, however, fortify the entire perimeter and are your best defense against malicious parties attempting to inappropriately access messages or data. While there are various approaches to implementing cryptography, many OEMs are taking advantage of the time-to-market and flexibility advantages of architectures like that found on the PrPMC815 with MPC185 security co-processor to quickly and cost effectively add both the performance and security features demanded by their VME customers.
Sidebar – shorter version
Processor PMCs Defined by VITA 32 Standard
PCI Mezzanine Cards (PMCs) have traditionally been considered an ideal method for expanding I/O due to their standard PCI interface and rugged mechanical mounting. As the size of processing cores shrinks, PMCs can now include a CPU. The VITA32, Processor PMC (PrPMC) standard describes this new "macro-component."
The guiding premise for the PrPMC standardization effort is to minimize the changes to the original draft IEEE 1386 and 1386.1 PMC standards. The PrPMC Standard is a 12-page document that complements these IEEE standards; it is available on the VMEbus International Trade Association (VITA) Web site (www.vita.com). Changes are required in just two areas:
- Redefine 15 of the 256 available signals (single-size PMC) to support the PMC as a master and target CPU rather than simply as an I/O device.
- Define a taller version to support CPUs with higher power dissipation.
Monarch initiates these changes
Two types of PrPMCs are defined. Due to the location of PCI clock and arbiter on the carrier, the terms monarch (host) and non-monarch (target) are introduced. The monarch is the main PCI bus PrPMC, this performs PCI bus enumeration following reset and also services PCI interrupts. A non-monarch is therefore not the main CPU. There must only be one monarch per system, while there can be as many non-monarchs as the electrical and thermal interface of the carrier will support. The new PRESENT signal positively identifies installed modules.
Changes to the interrupt signals were also required. The typical target PMC generates interrupt outputs, whereas a monarch acts as an interrupt handler requiring interrupts as inputs. The PrPMC draft standard therefore allows bidirectional interrupts.
The PCI specification supports 66 MHz operation so M66EN has also been included. The PMC specification defines only one PCI load per PMC. The PrPMC draft standard allows two loads on a PrPMC, similar to the two-load option that is available to the CompactPCI system slot.
Mechanical changes
The Processor PMC standard defines a new tall option, which may be required to accommodate heat sinks for CPUs with increased power dissipation. An increase of 20mm in height is a natural choice, since tall PrPMCs can easily fit in two VME or two CompactPCI slots.
Similarly, the original PMC standard defined a power limit of 7.5 watts for a singlewide standard PMC. However, the current draft standard provides more realistic guidelines that allow the PrPMC and carrier/enclosure vendors to specify maximums based upon layout and thermal characteristics.
Greg Novak is Marketing Manager for Motorola Computer Group’s Processor PMC and Data Board families, including product definition, management, and marketing. In addition to providing day-to-day lifecycle support, Greg promotes medical and embedded architectures with a variety of published articles and seminars. He also focuses on standards-based embedded solutions as the committee chairman and/or editor for a several mezzanine standards including VITA 32 Processor PMC, VITA 39 PCI-X on PrPMC/PMC, and VITA 42 high-speed PrPMC/PMC.